Security
Steps ecoATM Takes To Optimize Security
The ecoATM® kiosks were designed to be easy and efficient for use by consumers, but behind the scenes is state-of-the-art technology that includes advanced machine vision, electronic diagnostics, and artificial intelligence. Moreover, the kiosk is composed of extensive security features and processes to deter the sale of any stolen devices and assist law enforcement in investigating and prosecuting suspected cell phone thieves.
Learn more about our many security initiatives and law enforcement assistance tools and processes below:
It’s often thought that ecoATM kiosks operate completely on their own, but no transaction can be completed without the approval of a live verifier. Using the three-high resolution webcams on the kiosk, ecoATM employees located in the company’s headquarters monitor and approve every transaction in real-time.
Watch the video below for a first-hand look at our live verification security processes:
Live Validation Steps:
ecoATM kiosks use AssureTec ID technology to electronically verify that an ID is legitimate. AssureTec's high-resolution scanners can spot the telltale signs of a counterfeit ID invisible to the naked eye. After the AssureTec ID electronically verifies the government issued ID for authenticity by examining the ID for holograms, watermarks, or other specific identification methods, the customer is permitted to proceed. However, this does not yet mean the customer has been approved to complete a transaction.

1.While the ID is being verified for authenticity, the machine scans and captures photos of the ID. Using the kiosk's built-in webcams, the remote attendant compares the photo ID with the user's face in real-time to confirm their identity.
2.The remote attendant also verifies that the ID hasn't expired and that the customer is over 18 years of age.
A transaction will be denied by the attendant if:
Consumer is not in view

Blocked Camera
If our cameras are obstructed, the attendant will instruct the consumer to remove any items that may obstruct our view. If any of the cameras are obstructed, we will deny and request the customer re-center themselves so we can capture clear photos.

Face does not match ID

Device Security Check
Before ecoATM kiosks purchase any valuable device, the kiosk will check the device's uniquely identifying serial numbers through the service CheckMEND.com to determine if the device has been reported stolen. CheckMEND compiles records from carriers, police, the FBI, and more to create a comprehensive database of stolen devices on an international scale. If the device is does not pass CheckMEND's background check, the ecoATM kiosk will reject the transaction.
Additionally, all ecoATM® kiosks are equipped with security cameras that assist remote attendants in the Live Validation process, as well as capture security still images that may also be turned over to law enforcement upon request.
Why CheckMend?
Learn about how CheckMEND equips ecoATM to avoid lost, stolen, or compromised devices.
Please review the following information to learn more about recent issues, research, and how our machine works.
• Berkeley Research Group Report – Has the Presence of Smartphone Recycling Kiosks in Major U.S. Cities Affected the Incidence of Robbery and Larceny?
• ecoATM Law Enforcement Packet
• ecoATM Law Enforcement Awards and Partnerships
Ability for police to open kiosk
Law enforcement personnel who need access to a device inside the kiosk can simply call ecoATM and we can open the door remotely at any time. Once an officer's ID and law enforcement credentials have been validated, the front door of the kiosk will be automatically opened and a specialist will be available to help secure the device you are looking for.
Return of reported stolen items
ecoATM will respond quickly and diligently to any request from law enforcement to research and/or return reported stolen devices that may have been collected by the kiosk. Any reported stolen devices will be returned with no subpoena or search warrant required and at no cost to the victim.
30-day inventory hold
ecoATM holds all inventory collected for a minimum of 30 days. We will hold inventory for longer if required. Once the hold period has passed, we ship the devices to our recyclers from our processing center in Louisville, Kentucky.
"Do Not Buy" List
ecoATM works with law enforcement to implement a "do not buy" list, which bans individuals from utilizing an ecoATM® kiosk. Additionally, if an individual is identified by law enforcement as having sold a stolen device at an ecoATM kiosk, we electronically "ban" that individual from conducting further transactions at ecoATM kiosks.
No warrants or subpoenas
We do not require a search warrant or subpoena, and we will provide any device(s), associated records, and security camera still images to law enforcement in our possession upon request. If any officer has an investigative interest in a device that is currently deposited in one of our kiosks, they may simply visit the kiosk, call us and present their credentials to the kiosk camera, and we will remotely open the kiosk to allow the officer to recover any device.
Device Flagging
If you call or email our Regulatory Affairs Department, we can check IMEI/MEID and hardware serial numbers in our system to determine if a specific device was received by ecoATM. If the device in question has not been received by ecoATM, we can create an automated flag which will alert us and enable us to alert you if the device is recycled at an ecoATM kiosk.
Second Hand Dealer Laws
ecoATM offers an open book policy to all law enforcement that can use the information we have to assist in an investigation. We can report transactions in any method preferred such as Business Watch International, Pawnweb, Finder, NEWPRS, LeadsOnline and more. We can be contacted by sending an email to regulatory.affairs@ecoatm.com (email is monitored Monday through Friday, during business hours (PST) ) and we’ll get back to you.
• Full transparency
• We'll report in whatever method preferred
• Easy access to photos, serial numbers, and other information about sellers
LeadsOnline Partnership
In 2013 we created a partnership with LeadsOnline that will offer all officers access to ecoATM kiosk transaction reports on LeadsOnline free of cost. LeadsOnline is a nationwide web-based investigative system that law enforcement can use to access, print and search their local ecoATM transactions easily and quickly.
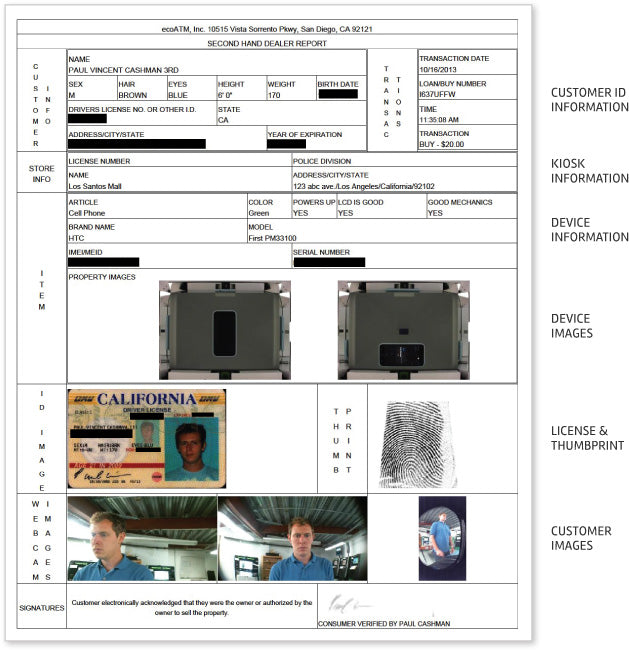
Sample Transaction Report
ecoATM is certified under the ISO 27001 standard for our information security management system (ISMS). An ISMS is a framework of policies and procedures that includes all legal, physical, and technical controls involved in securing company information. This helps ensure that ecoATM protects consumer data, employee information, financial accounting, third party information, and intellectual property across all systems and networks.

